
Spyware is a double-edged sword. On the one hand, they can help parents protect their kids, law enforcement catch criminals, employees keep track of employee productivity, etc. However, their wide availability and their aggressive marketing are quickly eroding the gains that their technology has brought to our society.
Anyone with malicious intentions – pedophiles, hackers, and cybercriminals – can just Google ‘hidden spy apps for Android,’ purchase a subscription, and access tools revealing all the information they need on their prey.
According to the Coalition Against Stalkerware, stalkerware is now being used to “facilitate intimate partner surveillance, harassment, abuse, stalking, and/or violence.” Most spy software for the iPhone uses stealth technology that tracks every activity on the phone without leaving the slightest clues.
This stealth operation makes it harder not only to learn how to find out if your phone is tapped but also to track down and prosecute your assailant. Because it makes it easy to perpetrate crimes and get away with it, spyware emboldens cybercriminals, leading to increasing rates and intensities of harassment and cyberviolence across parts of the world.
A recent report by the European Institute for Gender Equality shows that 7 in 10 women in Europe who’re victims of cyberstalking have suffered some form of physical or sexual violence. There are even more disturbing statistics.
In this dossier, we examine the impact of the rising use of spyware on our society today. Also, if you think you may be a victim of spyware, we’ll show you effective spyware removal tips to help you lose your stalker.
What Is Spyware and Stalkerware?
Spyware are stealthy, lightweight tracking algorithms that lock into a target phone’s operating systems to drill data. They can operate round the clock without using up any significant amount of phone resources, generating junk files with suspicious names, or displaying suspicious icons anywhere on the phone.
With unfettered access to every data saved on the phone, spyware lets users view everything from their target’s messages to call logs, browser data, social media activities, and lots more. Users enjoy remote access to their target’s phone data, logging into the spy app from their devices to check up on updates of their target’s activities whenever they want.
These devices are becoming increasingly ubiquitous, making it increasingly imperative for people to learn how to stop someone from spying on their cell phone. Far from their original purposes, spy apps are now being put to use in an ever-increasing variety of ways – including disturbing ones.
The following statistics from Kaspersky – a global leader in the antimalware industry – paint a riveting picture of the rising prominence of spyware in our world today:
- In 2018, a total of 40173 cases of spyware were reported across the globe, according to Kaspersky’s caseload.
- In 2019, that figure nearly doubled, clocking 67,500 global cases.
- As activities across different spheres came to a screeching halt at the height of the pandemic in 2020, the use of spyware continued in full swing. At 53,870 cases, the 2020 figure fell just shy of the all-time high from the previous year – perhaps tapered by the effects of the lockdown.
- Among those cases, Nidb – vendors behind popular names of spyware programs on android like TheTruthSpy, iSpyoo, and Copy9 – had the largest number of cases among individual vendors, fingered in some 8,100 cases.
The bulk of cases were recorded in the Russian Federation, Brazil, and the USA.
Here’s how cases were spread across the world in 2020:
| S/No | Country | Affected Users |
| 1 | Russian Federation | 12389 |
| 2 | Brazil | 6523 |
| 3 | USA | 4745 |
| 4 | India | 4627 |
| 5 | Mexico | 1570 |
| 6 | Germany | 1547 |
| 7 | Iran | 1345 |
| 8 | Italy | 1144 |
| 9 | United Kingdom | 1009 |
| 10 | Saudi Arabia | 968 |
Note, however, that these figures represent only cases reported by Kaspersky’s unique users and therefore portray only a fraction of cases in real life.
Why Is It Dangerous?
Stalkerware is a powerful tool that leaves sensitive information about people’s lives in plain sight. Their ready availability poses serious social risks in today’s digitally supercharged society – a fact well-documented in numerous cases of domestic violence, intimidation, harassment, and cyberviolence.
In the UK, for example, a report from Women’s Aid – a platform for underserved or abused women – suggests that, in 2018, nearly 1 out of 3 cases of abuse involved the use of spyware. It’s even worse in countries like Australia, where a 2015 Recharge survey of domestic violence practitioners shows that 74% of victims of abuse experienced “tracking via smartphone apps.”
In many of these cases, partners – sometimes also children – are murdered by their significant others. Their partners use stalkerware to track them down to a place where something phony might be happening, and then things fly off the handle.
As a parental monitoring instrument, spyware can actually do more harm than good to parent-child relationships. It’s no wonder parental control apps and how to know if your phone is being tracked have become hot-button issues for most parents in recent times. A study in 2015 suggests that most parents balk at the idea of monitoring their kid’s phones, denouncing the invasion of kids’ privacy.
Many parents feel parental control apps could undermine their kid’s trust in them, creating long-term issues in their parent-kid relationships. Even the United Nations have weighed in on the issue, seeking to prevent “potentially abusive form of surveillance” of children by parents or guardians.
In the workplace, even when it’s used legitimately or legally, spyware can easily give rise to disenchantment and dissatisfaction among employees. Employees under such close surveillance usually feel their privacy has been violated, and they’re being treated unfairly.
What Are The Most Popular Spyware Apps?
Stalkerware is a dime a dozen these days. They come in all forms, shapes, and sizes, offering varying selections of phone tracking features and functionalities.
However, statistics show that a few long-standing vendors account for significant market shares.
The most predominant spy apps today include:
mSpy

You’ll find mSpy on most top spy app lists on the web. The app has been around for quite some time and continues to expand its offerings by the day. It currently offers one of the most comprehensive phone tracking packages, replete with both basic and highly advanced features.
Users can use mSpy to track their target’s calls, text messages, activities across nearly all popular social media platforms, browser activities, plus lots more.
mSpy does all of this with a stealthy algorithm that’s invisible to the untrained eye. If you don’t have steep experience with stalkerware or don’t have antivirus protection on your phone, your chances of stumbling on noticeable signs of spy apps like mSpy on your phone are nearly nonexistent.
iSpyoo

iSpyoo is one of those longstanding apps that have managed to survive the stiff competition and the high demands of customers in the space. They’ve had their own fair share of poor reviews and dissatisfied customers, but they’ve managed to maintain a solid reputation.
Initially, the app’s main drawback was that it wasn’t stealthy enough, giving many users away quite easily. However, the creators have upgraded the software to a super-stealth machine, in addition to a host of other feature enhancements rolled out over the years.
The app also packs a punch of phone tracking features. It sorts a wide range of phone data into easy-to-follow categories, with each category presenting comprehensive details of related activities.
For instance, the text data lets users see not only the content of the text but the time and date stamps and contact details of the correspondents. Call data lets you see the top 5 frequently dialed numbers as well as the time and date stamps of the calls.
However, there have been numerous reports that the user interface is unstable, and users cannot access many of the app’s features.
Cocospy Brands
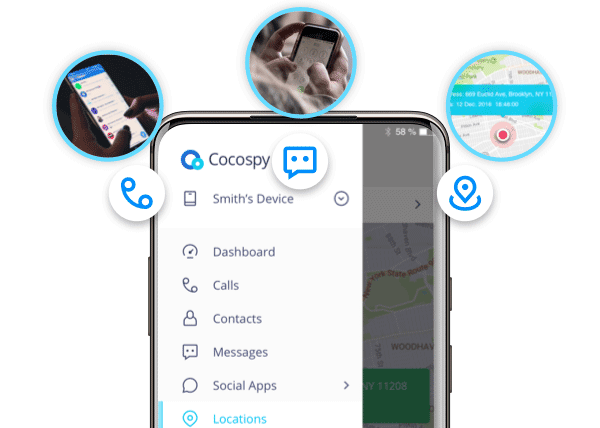
With over a million customers sprawled across over 190 countries, Cocospy and its sister apps enjoy some of the highest levels of patronage in the industry. From parents to employers, security personnel, and even government operatives, the app boasts a wide user base that cuts across different segments of our society.
The popularity of the apps is largely a result of the solid parental control features they provide. The apps give users remote track and control capabilities for a wide range of phone activities, from calls to texts, activities on various apps – including social media apps, browsing history, etc.
FlexiSPY

FlexiSPY is another top-rated spy app that lines up a wide array of tracking features ranging from basic to highly advanced. They even offer highly controversial features like call recording, which is outlawed for anyone other than law enforcement in most countries like the US and UK.
Other notable features include remote ambient recording, which lets users listen in on their target’s offline conversations, and remote screenshots, which lets users view their target’s screen in real-time, all from a remote location.
These features all violate wiretapping and video recording laws in most countries. However, the vendors make a brazen attempt to warn users against violating local laws, stating on their website that users do so solely at their own risk.
How Are Spyware Apps Marketed?
At face value, spy apps are often presented as innocuous products that can help people protect their families and relationships. However, if you read between the lines, you can’t help but notice some contradictions in the marketing materials of most spy apps.
Let’s take a critical look at some of these mixed messages:
Parental Control Doesn’t Usually Mean Kids Protection
It’s all fine and dandy to put powerful remote control features out there for parents who need to regulate their kids’ phone activities. But what happens when parents share equal access to these control features with malicious actors they’re trying to protect their kids from? Parental control apps often ignore this reality in their marketing.
One vendor guilty of this deliberate misrepresentation is the creator of the Cocospy brands. Apps from this vendor include Spyic, Neatspy, Minspy, Spyier, etc., and they’re all marketed as family-oriented parental control apps.
Another vendor is the maker of iSpyoo – an app that’s also repackaged into different products like Copy9 and TheTruthSpy.
Now, while these vendors hype up the benefits of these monitoring features for parents, they go mute on how they protect people when these apps are used maliciously.
It’s Not to Be Used Without the Target’s Consent – But It’s Stealthy by Design
So, spyware vendors claim, on the one hand, their apps are designed for ethical use only. Users aren’t supposed to use it without the express permission of their targets. But on the other hand, the apps are designed to go undetectable on the target’s phone, making it difficult to learn how to detect malware on an iPhone if you’re a victim.
Incredible capabilities for tracking a wide variety of phone data in stealth mode are entirely anathema to consensual tracking. Why would a vendor offer ‘stealth tools’ when they’re clearly against tracking someone behind their back?
Tracking Tools or Hacking Tools?
Another cringe-worthy misrepresentation you’ll find in stalkerware marketing is how ‘tracking’ and ‘hacking’ are used interchangeably. While tracking might imply some level of consent from the target, hacking absolutely revolves around doing something outside the target’s consent.
Some vendors support brute hacking techniques, which hackers use to force access to someone’s account. For example, FlexiSPY, which is marketed primarily as a ‘monitoring app,’ comes with ‘spoofing’ features, used to mislead people into doing things they’d otherwise not.
So much so for an app whose primary goal is to help users watch over a child, employee, or relationship partner.
Before signing up for the app, users are even required to “acknowledge that you will only install the software on a device which you have a legitimate need to monitor, and have a legal right to do so.” So why support hacking?
No Word on Potential Victims?
Another major moot point in spyware marketing is the invisibility of spyware victims to vendors. Marketing messages emphasize the capabilities available to users/operators. Meanwhile, nothing is said about people who may fall victim to the malicious use of these apps or who’re wondering, “Is my phone being tracked by someone?”
We’re not just talking about kids, but partners, employees, members of the general public. Every day, people have their data collected and stored on stalkerware databases, made accessible to anyone for a price, without their prior consent. Spyware vendors keep silent over this, focusing only on promoting their ‘hidden,’ ‘stealthy’ tracking features – with little or no regard for who the users or target might be.
How Spyware Is Installed on Target Smartphones?
Another major reason why skalkerware are becoming increasingly popular is their ease of use. With spy apps, there are no technical barriers to tracking others’ phones. You simply need to follow an easy guide. The installation process is usually automated for the most part.
Android Installation
Android phones require a little more effort. Physical access to the target phone is required at least once – just to load a link that’ll trigger an automatic download and installation. This usually takes just a few minutes.
Here are the steps usually required:
Step 1. Sign Up for the Spy App
The first step is launching the vendor’s website and purchasing a subscription. This can take a couple of minutes, and handing out some personal details.
Step 2. Download and Install the Spy App
The next step is following the instructions on the confirmation email for the app subscription. The instructions vary depending on the vendor but usually entail loading an automatic download and installation link on the target phone.
Note, however, that some features of spy apps require the removal of some factory-fit restrictions on the phone. This process is called rooting, but it might also give you clues of how to find hidden spy apps on Android (more on that below).
While this process enables certain tracking features, it can expose the phone to some serious security threats. Threats from third parties like hackers and stalkers – besides those contained in the spy app itself like malware and ‘nuissanceware.’
However, with the non-rooting or non-jailbreaking setup, users can still get a hold of a whole lot of sensitive data on the target phone, including social media activities and SMS.
Step 3. Collect Phone Data
Once the app is loaded on the target phone, everything else is a cakewalk for users. They can just log into their dashboard to scour through their target’s phone activities. Except the target is tech-savvy and vigilant, the tracking can go on for as long as the user needs to collect their data.
iOS Installation
For iPhones, it usually just takes entering your target’s iCloud ID and password on the user dashboard of the spy app. This enables the app to sync with the target’s iCloud account. Users will have access to their target’s iPhone activities so long as iCloud syncing is active on the target phone.
Here are steps in detail:
Step 1. Purchase Your Subscription
It begins with signing up for an account and purchasing a subscription on the vendor’s site.
Step 2. Load the Target’s iCloud Credentials
The installation instructions are sent to the email used to register the account but usually entail entering the target’s iCloud credentials somewhere on the user dashboard. Two-factor authentication needs to be deactivated on the target phone, except the secondary authentication device is accessible during the installation.
Note also that some important phone data will not be available on the target’s iCloud. To access those, the phone needs to be jailbroken – a process similar to rooting but for iOS devices. It creates access to a wider range of phone data, but at the expense of the phone’s security.
Step 3. Check for Data Updates
After that, the user can begin tracking their target remotely on any device. Depending on the frequency set for iCloud updates, they can log into their user dashboard from time to time to check for activity updates.
How to Detect Spyware on Your Phone?
Wondering how to find malware on Android? Here’s how to catch someone spying on you:
Critical Changes to Security Settings
One quick way to check if your phone is infected with spyware is by inspecting your factory security settings. If your phone has been jailbroken or rooted to install spyware, some notable factory-fit security settings will be inactive.
One good example is if the setting for downloading apps outside Google’s Play Store has been changed. That means you’re probably running some apps from unverified sources. The steps for checking this usually go like this: “Settings → Apps → Menu → Special Access → Install unknown apps.”
If you don’t know where to look, try using an Android spyware detection app. You’ll find many on Google Play Store.
On iPhones, check for container managers like Cydia, which are used to install apps on jailbroken iOS devices.
Phone Disappearing and Reappearing With Settings Changes
If your phone goes missing for a few moments then reappears, but with so many changes you’d swear someone’s tampered with it, your suspicions might just be true. Someone probably got a hold of it to set up spyware on it.
Phishing Messages
Another way to locate spyware on Android is to check for any odd, eerie messages sent to you via social media apps, email, or SMS. These messages usually sound urgent, poignant, curious, or undeniable. They could be about payments, promos, or security updates.
You’ve probably already clicked on such links, and your tracker could be following up on you with other tracking messages.
Don’t click any link ever again, and delete their carrier messages the moment you see them. Such links could lead you to either disclose some sensitive information like account credentials or to download spyware unknowingly.
Strange Apps in the App Drawer
Android.log.desk, CaptivePortalLogin, com.android.YGPS.Tracker. If you find files like these with name variations relating to tracking, logging, monitoring – especially if they’re third-party app files with unknown origins – you could be staring at Android spy app file names.
But you should also look out for apps with generic, less suspicious names. In short, it’s advisable to ditch any app, familiar or strange, that’s otherwise useless or hasn’t been used for a long time.
Antivirus Scan
An antivirus scan is a tried and true method of how to remove malware from the phone. Most stalkerware will pop up when you scan your device with a good antivirus.
Use a reputable product that’s very efficient – some spyware can easily evade antivirus scans with their lightweight, slippery nature.
How to Get Rid of Spy Apps?
Now, you’ll see how it’s easy to learn how to tell if someone is spying on your iPhone. But dislodging spyware usually requires frantic, pragmatic efforts. The difficulty depends on the nature of the spyware.
Here are some of the most effective ways to remove spyware from iPhone and Android phones:
- Use a malware remover. Most excellent antiviruses not only detect spy apps but also show you how to clean your iPhone from spyware.
- Activate two-factor authentication. Get notified whenever someone tries to access any of your important accounts from an unknown device.
- Change your passwords. After learning how to uninstall a hidden spy phone app and setting up login attempt notifications, the next thing you should do is change all your passwords – including your phone passcode. That’s so your tracker can never access your accounts or your phone with your old passwords.
- Update your OS. An OS update can instantly plug the entry ports of spyware.
- Push the full reset button. As a last-ditch effort, you can reset the phone to the factory state. This completely reverses everything done on the phone since it started getting used. Some useful things might be lost along with bad ones, but most spyware can hardly survive a hard factory reset.
- On Android phones, go to “Settings → General Management → Reset → Factory Data Reset.”
- On iOS, open “Settings → General → Reset.”
Is Spyware Legal?
Spyware vendors often try to skirt the lines of legality with End User License Agreements that require the users to acknowledge they’ll use the app with their target’s consent. They, therefore, absolve themselves of any legal repercussions when users deploy the apps in breach of applicable privacy laws.
However, the fact remains that spyware has been used – and abused – illegally in countless cases. And most spyware vendors are just not doing enough to prevent these illegal use cases, like setting up a response mechanism for victims who may be wondering, “Is my phone being monitored?”
Lawmakers in different regions across the world are working on tougher policies that will create more accountability in the industry. But government critics believe it’s less a matter of more new laws and more strict enforcement of existing laws.
They believe the government already has enough legal purview to take on not only people who use spyware illegally but the vendors who allow these illegal uses to occur right under their noses.

